Слайд 2Cryptography - data protection method
Derbyshev Lev
RI-270007
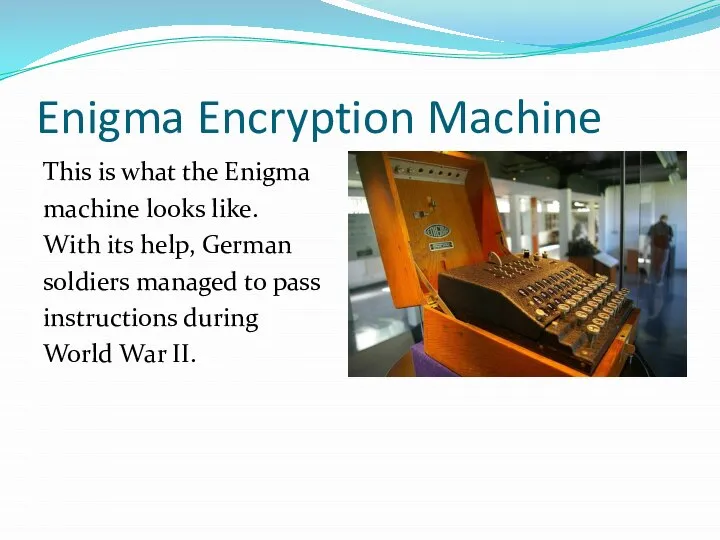
Слайд 4Enigma Encryption Machine
This is what the Enigma
machine looks like.
With its help, German
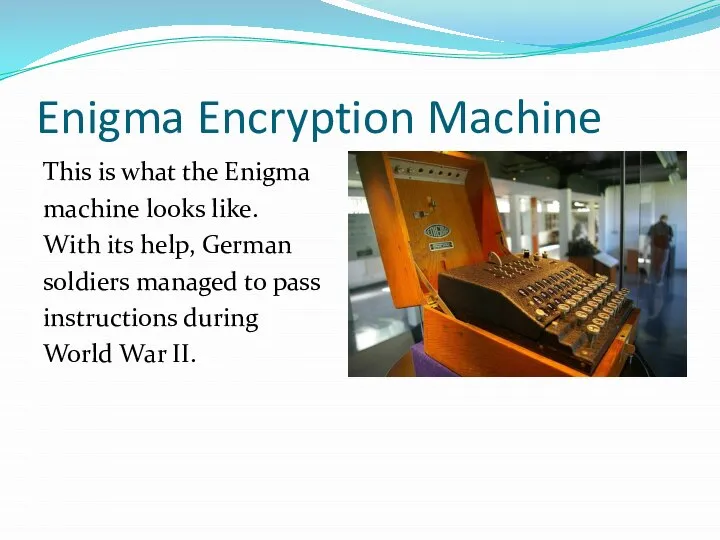
soldiers managed to pass
instructions during
World War II.
Слайд 5Information Problems
As the amount of data increases, the following problems appear:
Data leakage
Data
substitution
Distortion due to technical reasons
Слайд 6Personal data. Who is interested in this?
A lot of people search like
information. Its use may have a different character from the sale of a product to the actions of a criminal character.
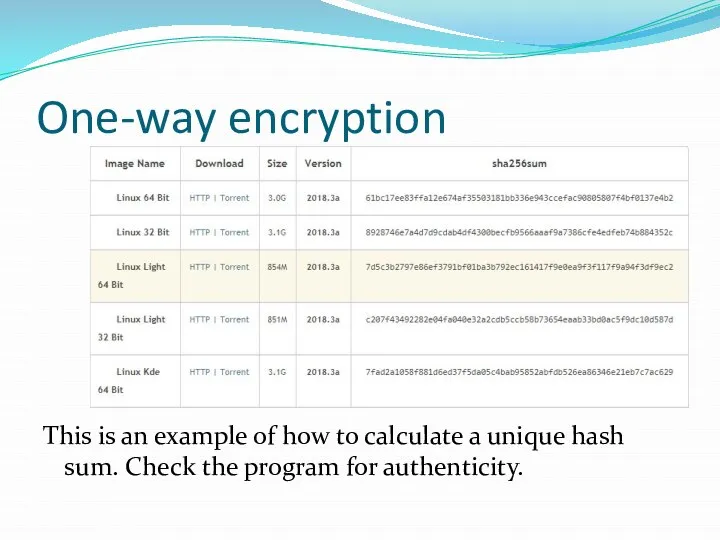
Слайд 7One-way encryption
This is an example of how to calculate a unique hash
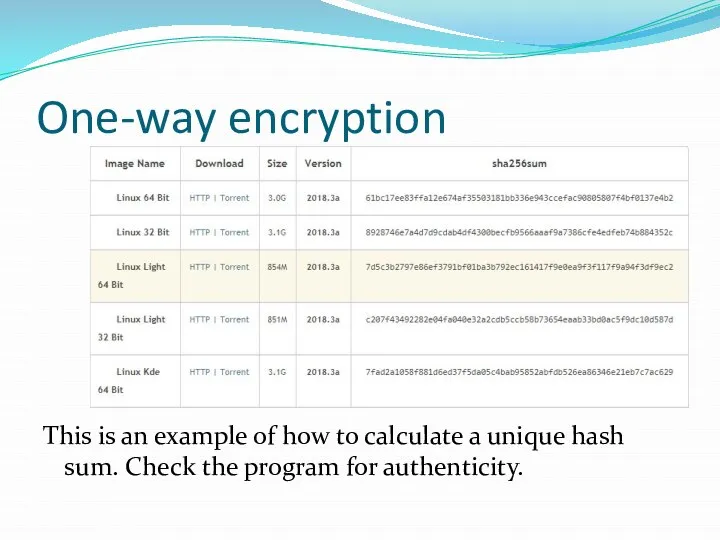
sum. Check the program for authenticity.
Слайд 8Two-way encryption
This type of encryption can be decrypted by knowing the master
key. It is designed to transmit data securely.
 His, her, our, your
His, her, our, your I asked my mother some questions about her school life and she told me about it
I asked my mother some questions about her school life and she told me about it Указательные местоимения
Указательные местоимения Haunted house
Haunted house Past Simple Past Continuous
Past Simple Past Continuous 1_14_PK_NOUN
1_14_PK_NOUN My Picture
My Picture Active or passive
Active or passive Свадебные приметы и предрассудки Wedding Superstitions
Свадебные приметы и предрассудки Wedding Superstitions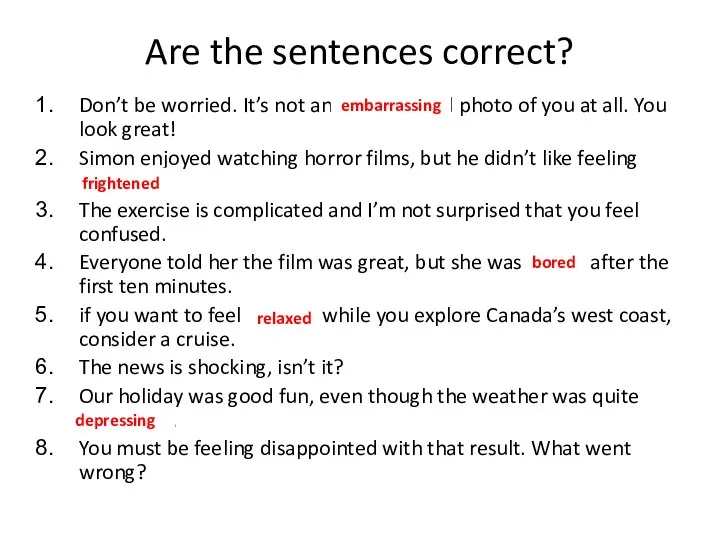 Narrative
Narrative Garfields daily routine
Garfields daily routine Let’s make a potion!
Let’s make a potion!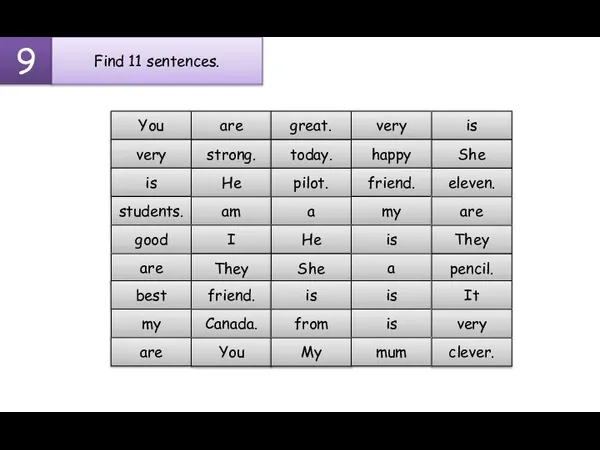 To be
To be Can i have some?
Can i have some? Microeconomics
Microeconomics Презентация на тему Age limits (Возрастные ограничения)
Презентация на тему Age limits (Возрастные ограничения)  Sea mammals
Sea mammals What is estuary english
What is estuary english Your Heart
Your Heart Презентация на тему АНГЛИЦИЗМЫ В МЕСТНОЙ ПРЕССЕ
Презентация на тему АНГЛИЦИЗМЫ В МЕСТНОЙ ПРЕССЕ  Презентация на тему Ирландия (на английском)
Презентация на тему Ирландия (на английском)  Why? Maybe you can say?
Why? Maybe you can say? Past perfect grammar
Past perfect grammar Syntax
Syntax Read the rubric and look at the key
Read the rubric and look at the key Present Simple practice. Lesson 24
Present Simple practice. Lesson 24 Какую букву рисует бабочка 2
Какую букву рисует бабочка 2 Spotlight 8 Module 2F
Spotlight 8 Module 2F