Содержание
- 2. The Discrete Log Problem The El Gamel public key cryptosystem is based upon the difficulty of
- 3. For a small value of p, it is easy to solve a DLP by trial and
- 4. El Gamel El Gamel is a public key cryptosystem with security which relies on the difficulty
- 5. El Gamel Key Generation Bob generates public and private keys as follows: He picks a large
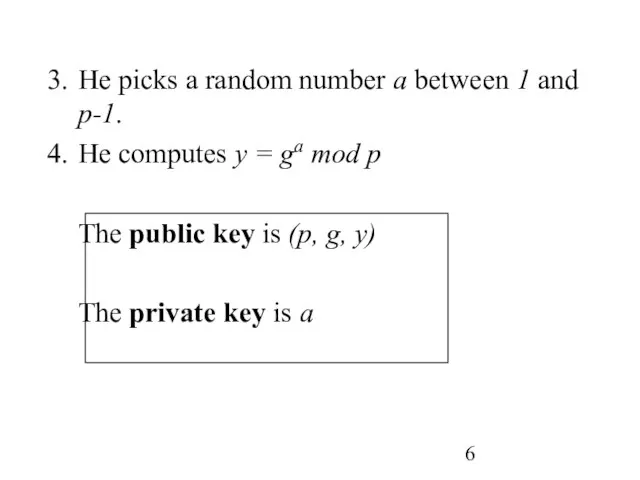
- 6. He picks a random number a between 1 and p-1. He computes y = ga mod
- 7. El Gamel Encryption If Alice wants to send Bob a message, she looks up Bob’s public
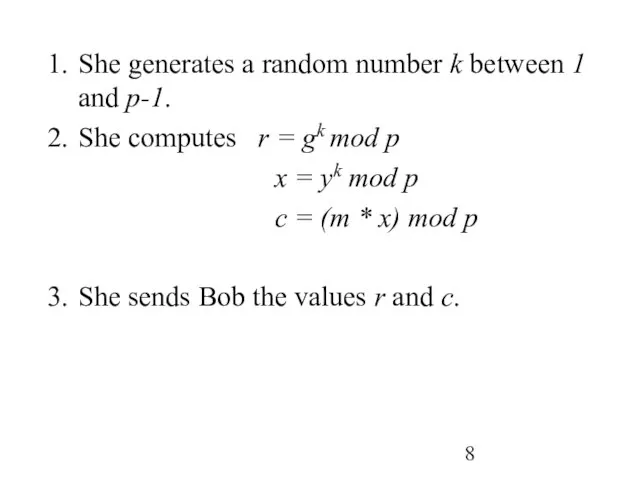
- 8. She generates a random number k between 1 and p-1. She computes r = gk mod
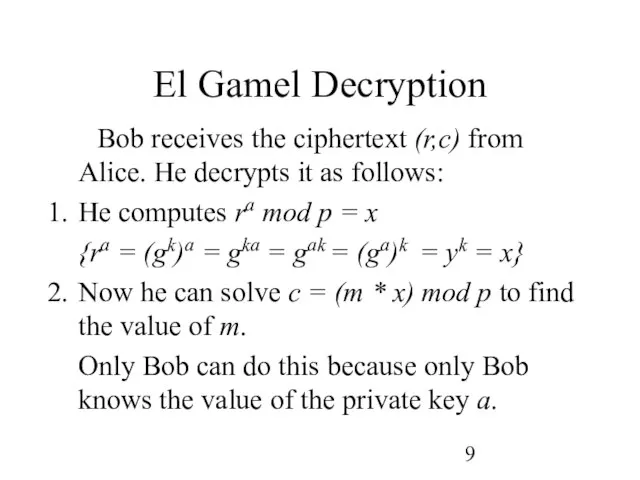
- 9. El Gamel Decryption Bob receives the ciphertext (r,c) from Alice. He decrypts it as follows: He
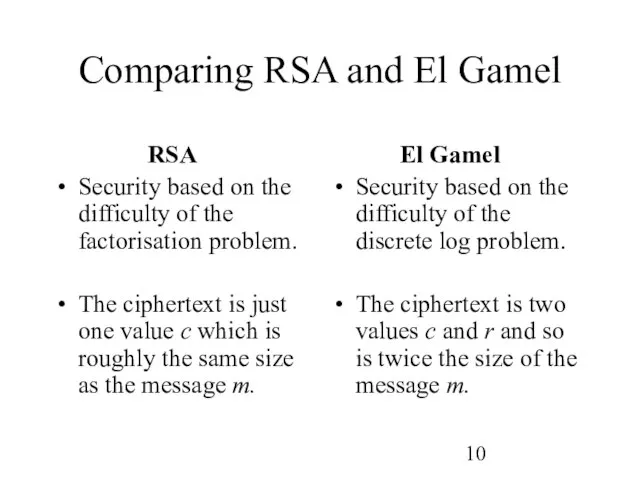
- 10. Comparing RSA and El Gamel RSA Security based on the difficulty of the factorisation problem. The
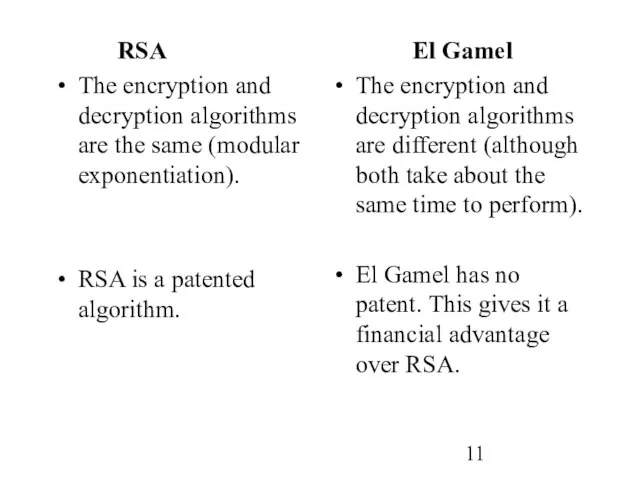
- 11. RSA The encryption and decryption algorithms are the same (modular exponentiation). RSA is a patented algorithm.
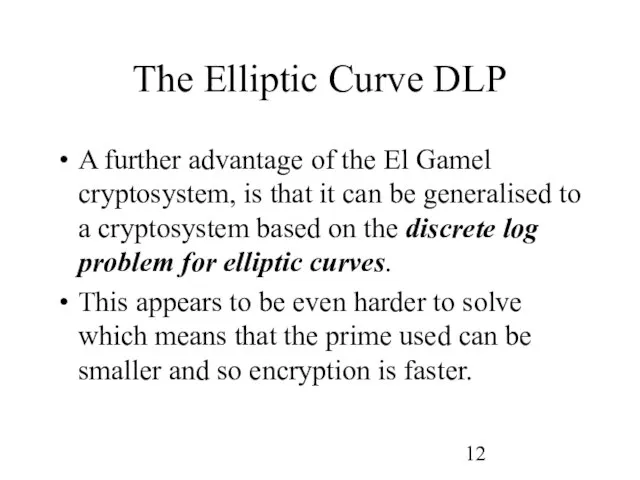
- 12. The Elliptic Curve DLP A further advantage of the El Gamel cryptosystem, is that it can
- 13. Applications of public key cryptosystems. Public key cryptosystems are generally less efficient but more secure than
- 14. Digital Signatures A digital signature for a message from a particular sender is a cryptographic value
- 15. To digitally sign a message m using a public key cryptosystem, Bob simply encrypts the message
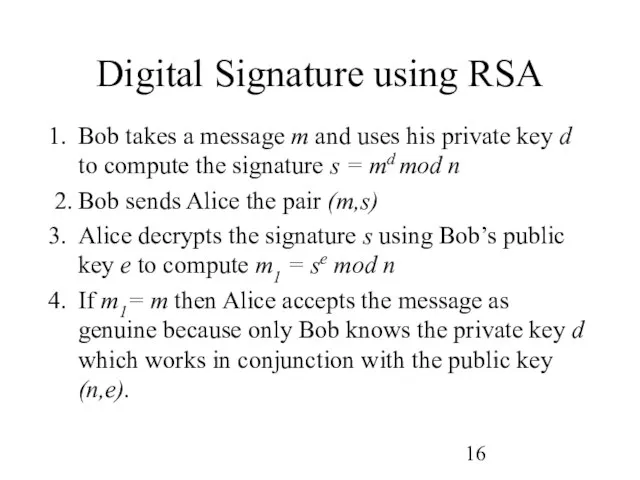
- 16. Digital Signature using RSA Bob takes a message m and uses his private key d to
- 18. Скачать презентацию
 Государственный и муниципальный кредит
Государственный и муниципальный кредит Подготовка к ГИА. Знаки препинания в сложносочиненном и сложноподчиненном предложении
Подготовка к ГИА. Знаки препинания в сложносочиненном и сложноподчиненном предложении Что такое постдемократия
Что такое постдемократия Возникновение искусства тату и профессии татуировщика
Возникновение искусства тату и профессии татуировщика Рабочая инструкция сборки формы “Вилка стойки” 12300-2905515-01 KURTZ
Рабочая инструкция сборки формы “Вилка стойки” 12300-2905515-01 KURTZ Стратегическая модель Ж. -М. Дрю
Стратегическая модель Ж. -М. Дрю 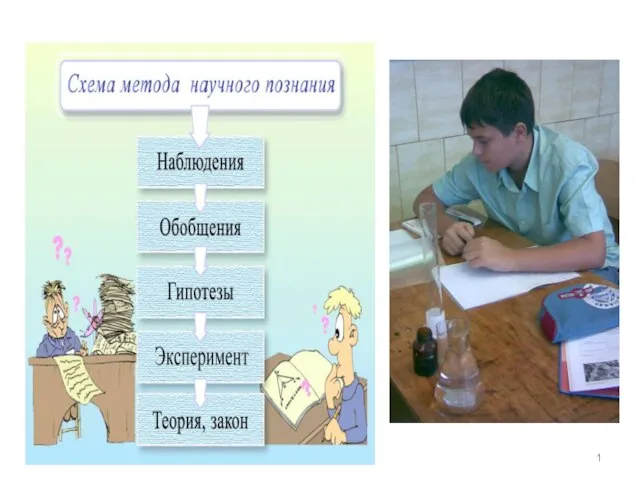 Презентация на тему Измерение физических величин
Презентация на тему Измерение физических величин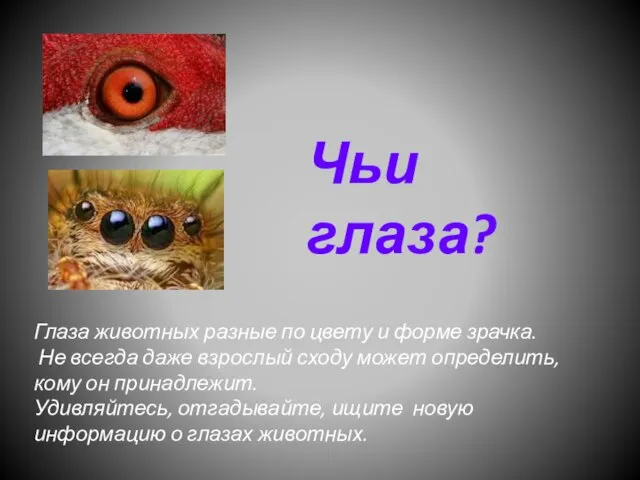 Чьи глаза?
Чьи глаза? «Шведский стол»
«Шведский стол» Иосиф Дик «Красные яблоки»
Иосиф Дик «Красные яблоки» Презентация на тему ПРОСТЕЙШИЕ
Презентация на тему ПРОСТЕЙШИЕ  Этикет 4 класс
Этикет 4 класс Произведения народного искусства
Произведения народного искусства Сравнительный анализ доходности индексных ПИФов и ПИФов акций
Сравнительный анализ доходности индексных ПИФов и ПИФов акций Presentation Title
Presentation Title  Die Geschichte des Fußballs
Die Geschichte des Fußballs Как мы общаемся с миром
Как мы общаемся с миром My favorite company
My favorite company Презентация
Презентация День правовой помощи детям
День правовой помощи детям Принятие решений в условиях существования рисков с низкими вероятностями реализации
Принятие решений в условиях существования рисков с низкими вероятностями реализации Письмо
Письмо Тактильная чувствительность
Тактильная чувствительность Инвестиция, как важнейшее условие для реализации проекта
Инвестиция, как важнейшее условие для реализации проекта Конструирование брюк
Конструирование брюк ПРОГРАМНЕ ЗАБЕЗПЕЧЕННЯ СПЕЦІАЛЬНИХ ІНФОРМАЦІЙНО-ТЕЛЕКОМУНІКАЦІЙНИХ СИСТЕМ
ПРОГРАМНЕ ЗАБЕЗПЕЧЕННЯ СПЕЦІАЛЬНИХ ІНФОРМАЦІЙНО-ТЕЛЕКОМУНІКАЦІЙНИХ СИСТЕМ Особенности продвижения транспортных услуг
Особенности продвижения транспортных услуг Священнослужители в рядах Русской армии
Священнослужители в рядах Русской армии