Содержание
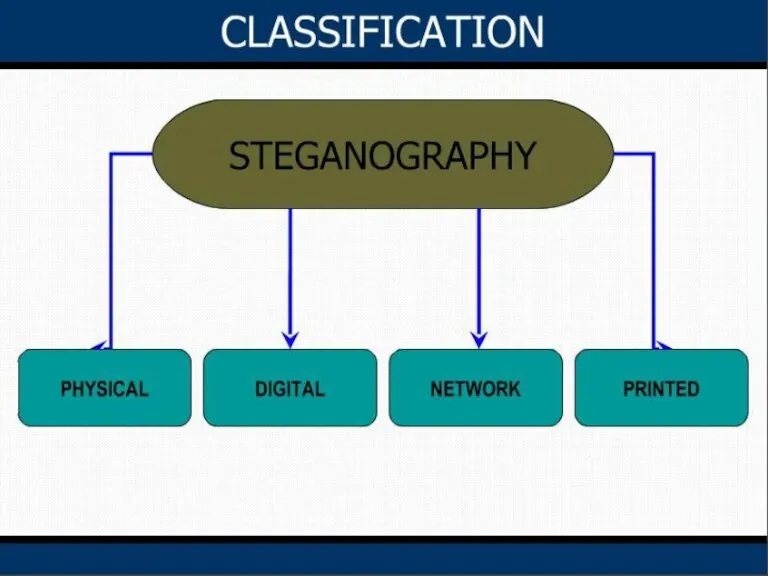
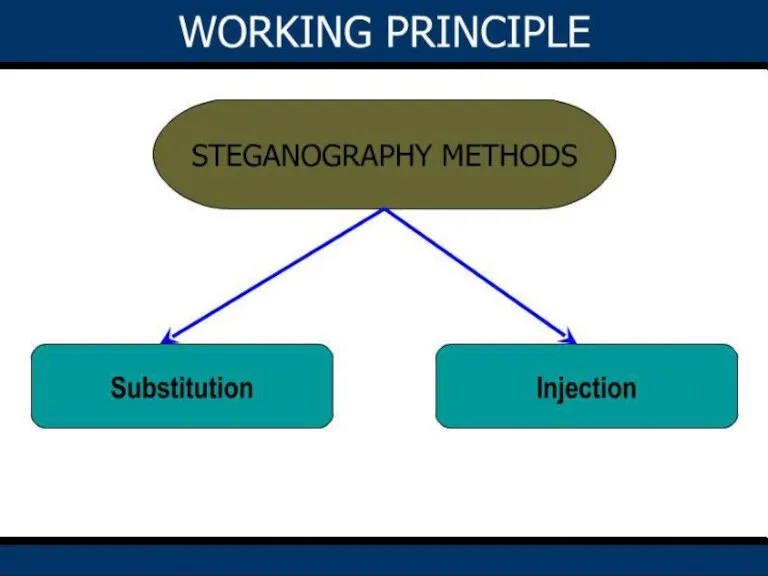
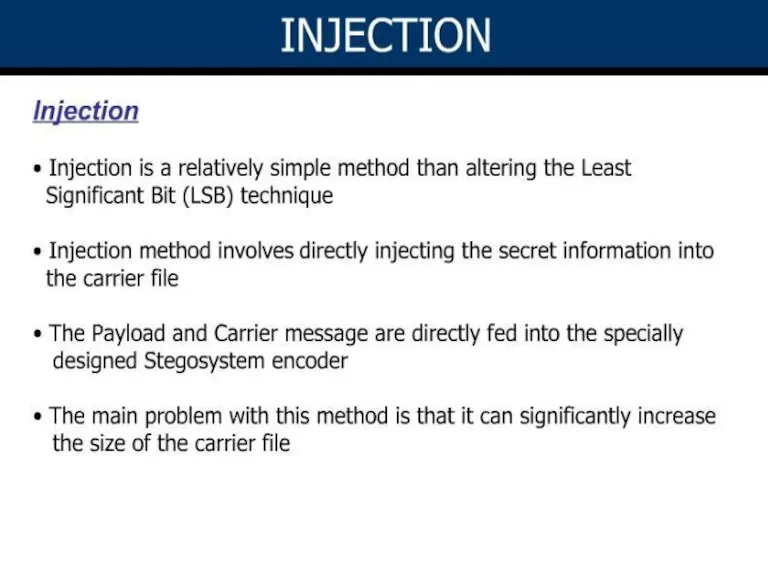
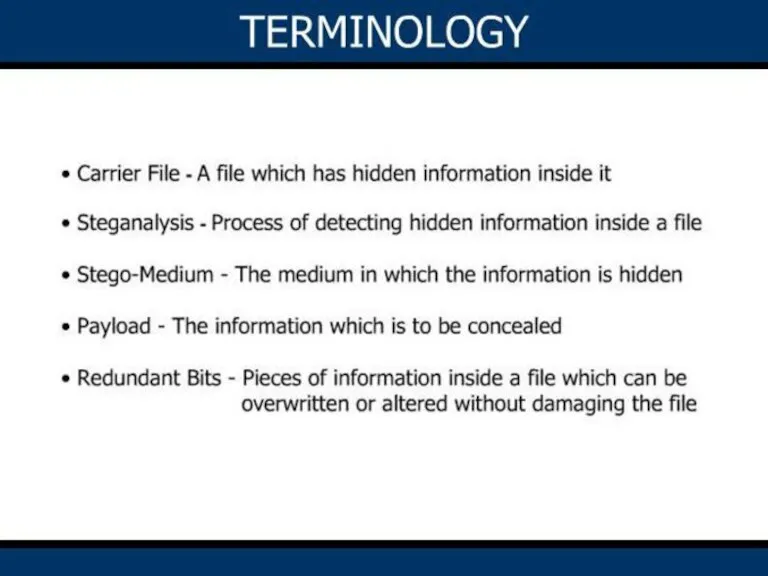
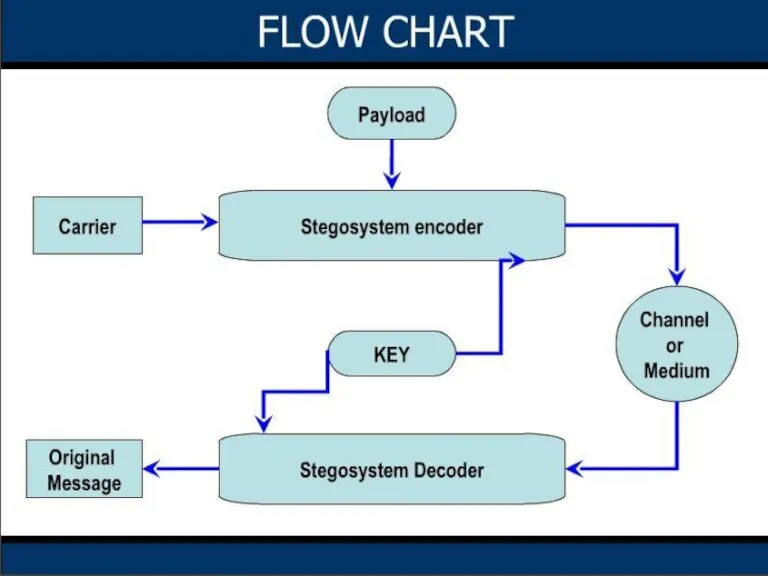
- 2. Introduction Steganography History Classification Working princple Least Significant Bit (LSB) Substitution Injection Flow Chart Steganography process
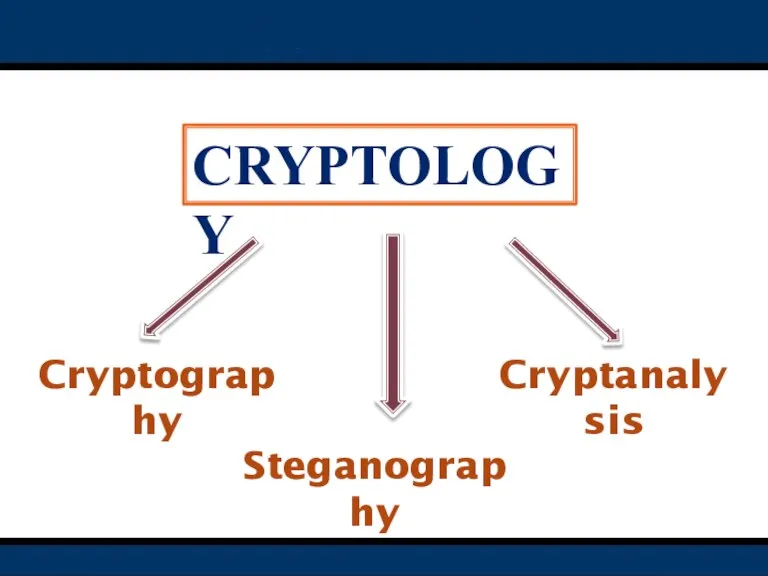
- 3. Cryptology Cryptography Cryptanalysis Steganography
- 12. STEGANOGRAPHY process Three basic ways to encode data in steganography: Image as a carrier Pixel representation
- 13. 1.IMAGE AS CARRIER: It is an efficient technique for steganography, An image is used as cover
- 14. 3.BANDWIDTH REDUCED TRANSMISSION: If an image data takes six minutes to transfer between two systems and
- 15. Two basic algorithms used for steganography Text on Image algorithm. Image on Image algorithm. BASIC ALGORITHMS
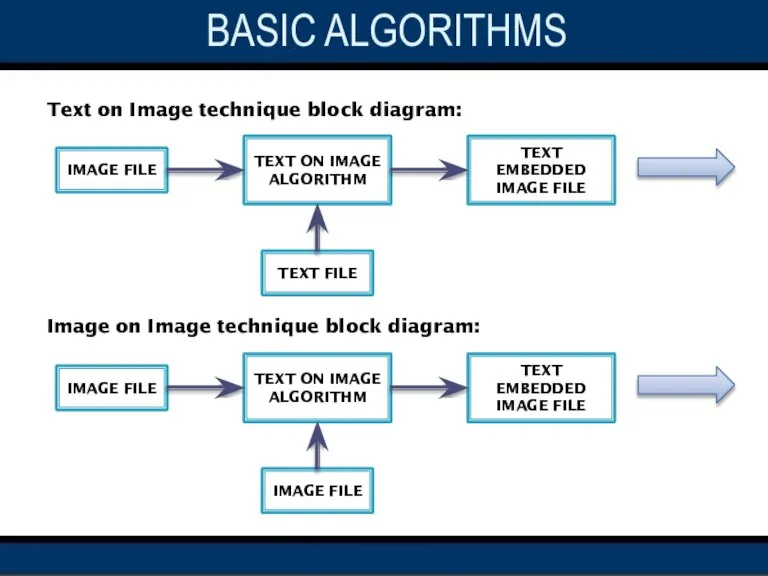
- 16. Text on Image technique block diagram: Image on Image technique block diagram: IMAGE FILE TEXT ON
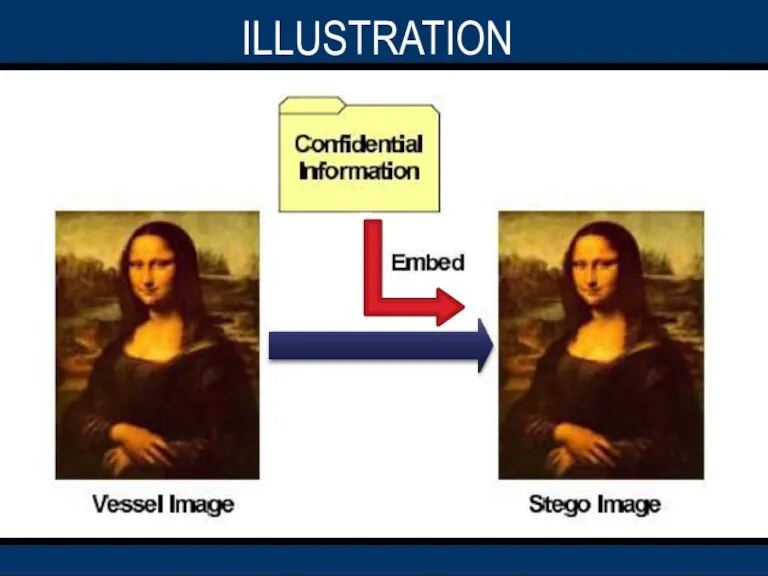
- 17. ILLUSTRATION
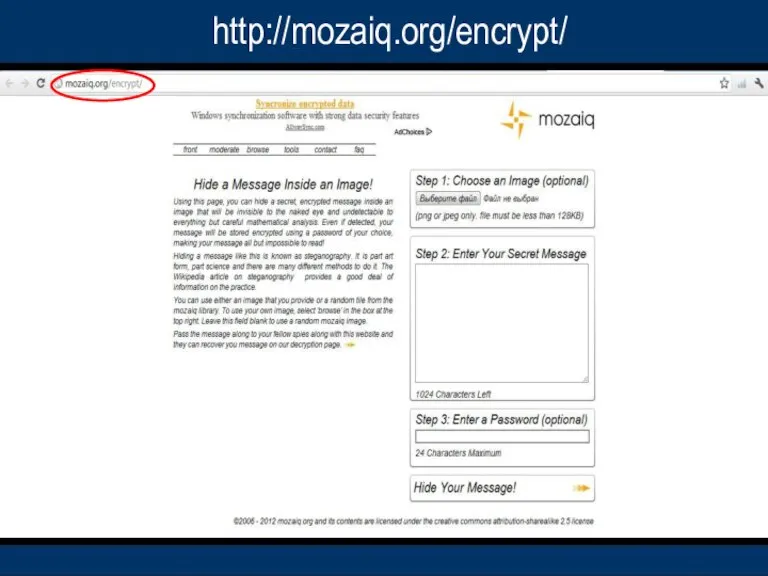
- 19. http://mozaiq.org/encrypt/
- 20. ADVANTAGES Internet privacy. Secret communication between the organizations like boarder security force and defense organization. Effective
- 21. ADVANTAGES
- 22. CONCLUSION
- 24. Скачать презентацию


 Образование в Финляндии
Образование в Финляндии «Развитие образования в МОУ «Аксаринская СОШ» на 2010-2012 гг.»
«Развитие образования в МОУ «Аксаринская СОШ» на 2010-2012 гг.» «СВОЯ ИГРА»
«СВОЯ ИГРА» Маркет-платформа
Маркет-платформа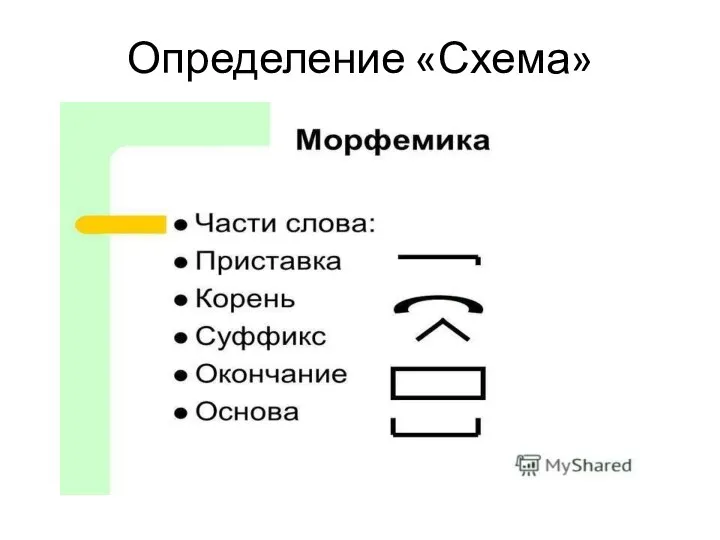 Электрическая схема
Электрическая схема Verbs in the kitchen
Verbs in the kitchen Российский Герб.История создания
Российский Герб.История создания Презентация на тему Деловые переговоры
Презентация на тему Деловые переговоры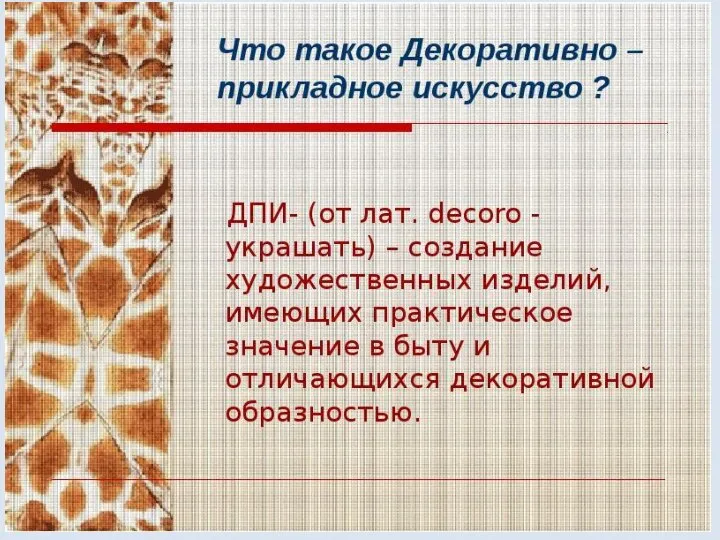 Что такое Декоративно - прикладное искусство
Что такое Декоративно - прикладное искусство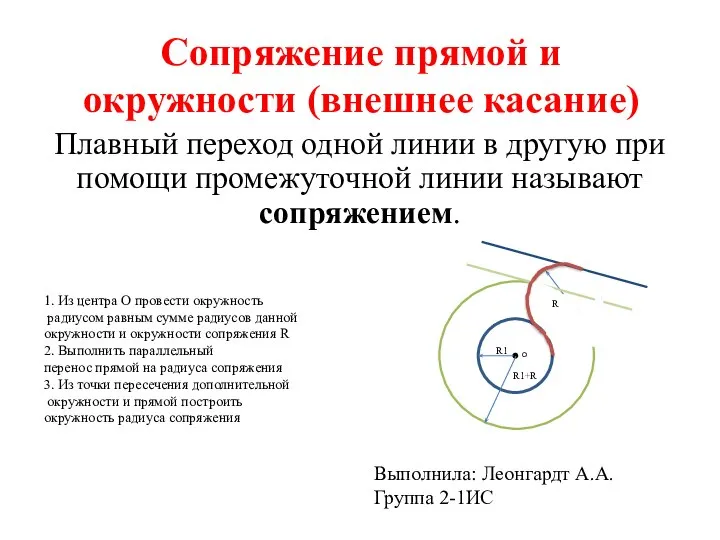 Практическая № 37-38
Практическая № 37-38 Mickey Mouse
Mickey Mouse БАКТЕРИИ (3 класс)
БАКТЕРИИ (3 класс) Направление подготовки Гидрометеорология. Кафедра гидрологии и охраны водных ресурсов
Направление подготовки Гидрометеорология. Кафедра гидрологии и охраны водных ресурсов Halloween. Traditions and Safety Tips
Halloween. Traditions and Safety Tips Русские народные промыслы
Русские народные промыслы Типы супружеских отношений
Типы супружеских отношений Теоретические основы безопасности жизнедеятельности
Теоретические основы безопасности жизнедеятельности  Инклюзивное развитие и становление творческой личности на занятиях вокалом для взрослых
Инклюзивное развитие и становление творческой личности на занятиях вокалом для взрослых Календарь мчс или безопасность глазами ребенка
Календарь мчс или безопасность глазами ребенка Коммерческая сделка (Тема 9)
Коммерческая сделка (Тема 9) Боги древней Индии
Боги древней Индии  Послеродовой тиреоидит
Послеродовой тиреоидит  Экономическое обоснование использования современных средств индивидуальной защиты
Экономическое обоснование использования современных средств индивидуальной защиты Творческий проект Толкушка
Творческий проект Толкушка ФГАОУ ВО СЕВГУ Морской колледж
ФГАОУ ВО СЕВГУ Морской колледж Региональная конкурентоспособность как важнейшая составляющая социально-экономического развития России
Региональная конкурентоспособность как важнейшая составляющая социально-экономического развития России Материальная ответственность сторон трудового договора
Материальная ответственность сторон трудового договора Развитие интеллектуального и творческого потенциалаобучающихся на уроках физики
Развитие интеллектуального и творческого потенциалаобучающихся на уроках физики