Содержание
- 2. Understand the core of Operations Security (OPSEC) Define & identify targets and threats Establish countermeasures Identify
- 3. What is Operation Security…? Have you ever taken precautions against Someone… …breaking into your house while
- 4. OPSEC is a risk management instrument that enables a manager or commander to view an operation
- 5. Identify Critical Information Analyze Threats Discover Vulnerabilities Assess Risks Develop Countermeasures What is Operation Security …?
- 6. Identify Critical Information: Credit card numbers, travel dates, passwords, patterns, changes in patterns, inspection results, information
- 7. Discover Vulnerabilities: Flow of information, operations, timing of events, how an adversary would acquire the information,
- 8. Develop Countermeasures: are based on the vulnerabilities and inherent risks. What is Operation Security …?
- 9. Viruses and Other Malicious Content computer viruses have got a lot of publicity one of a
- 10. The Most Common Types Of Program To Be Infected by A Virus exe com vbs Mp3
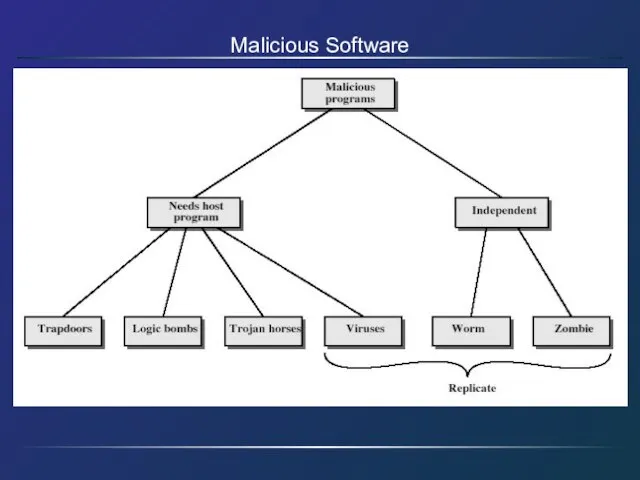
- 11. Malicious Software
- 12. Trapdoors secret entry point into a program allows those who know access bypassing usual security procedures
- 13. Logic Bomb one of oldest types of malicious software code embedded in legitimate program activated when
- 14. Trojan Horse program with hidden side-effects which is usually superficially attractive eg game, s/w upgrade etc
- 15. Zombie program which secretly takes over another networked computer then uses it to indirectly launch attacks
- 16. Viruses a piece of self-replicating code attached to some other code propagates itself & carries a
- 17. Virus Operation virus phases: dormant – waiting on trigger event propagation – replicating to programs/disks triggering
- 18. Types of Viruses - can classify on basis of how they attack parasitic virus memory-resident virus
- 19. Macro Virus macro code attached to some data file interpreted by program using file eg Word/Excel
- 20. Email Virus spread using email with attachment containing a macro virus triggered when user opens attachment
- 21. Worms replicating but not infecting program typically spreads over a network using users distributed privileges or
- 22. Worm Operation worm phases like those of viruses: dormant propagation search for other systems to infect
- 23. Virus Countermeasures viral attacks exploit lack of integrity control on systems to defend need to add
- 24. Summary have considered: various malicious programs trapdoor, logic bomb, trojan horse, zombie viruses worms countermeasures
- 25. Public Key Cryptosystem Essential steps of public key cryptosystem Each end generates a pair of keys
- 26. RSA (public key encryption) Alice wants Bob to send her a message. She: selects two (large)
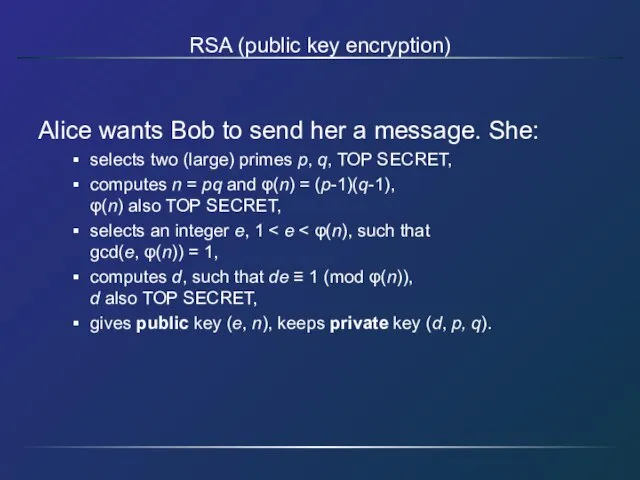
- 27. RSA Example Select primes: p=17 & q=11 Compute n = pq =17×11=187 Compute φ(n)=(p–1)(q-1)=16×10=160 Select e
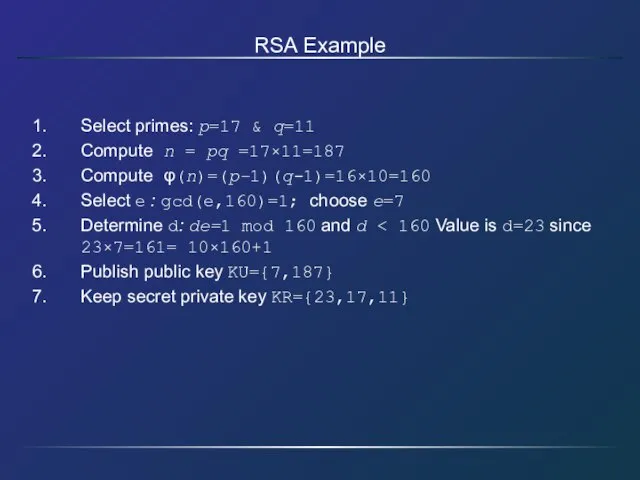
- 28. RSA Example cont sample RSA encryption/decryption is: given message M = 88 (nb. 88 encryption: C
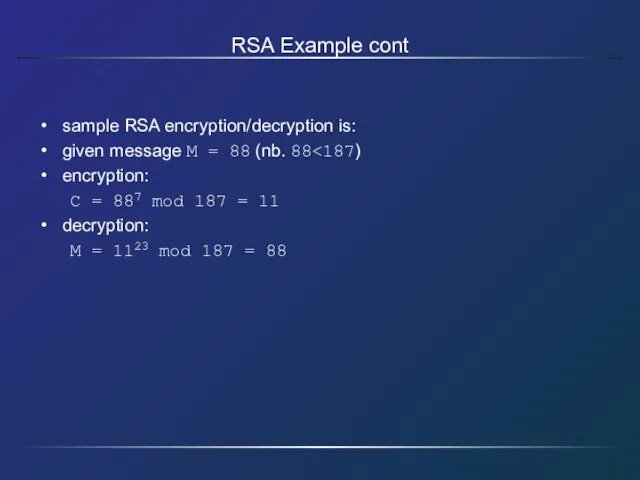
- 30. Скачать презентацию
 Украина
Украина  Buckingham Palace
Buckingham Palace Бизнес-планированиеЗанятие 4
Бизнес-планированиеЗанятие 4 Интеллектуальная электроэнергетика
Интеллектуальная электроэнергетика Поработайте над содержанием презентации:
Поработайте над содержанием презентации: Санкт-Петербургский технический колледж управления и коммерции СПб ТКУиК
Санкт-Петербургский технический колледж управления и коммерции СПб ТКУиК Культура Византии
Культура Византии Презентация на тему Обоняние и вкус
Презентация на тему Обоняние и вкус История создания романа Ф.М. Достоевского «Преступление и наказание»
История создания романа Ф.М. Достоевского «Преступление и наказание» Повторение пунктуации сложного предложения. Знаки препинания в БСП
Повторение пунктуации сложного предложения. Знаки препинания в БСП Представление
Представление Вступительный экзамен в СНК “Эскулап”
Вступительный экзамен в СНК “Эскулап” Цветок — Нарцисс
Цветок — Нарцисс Охрана здоровья и безопасностьИТОГИ 2008 годаОАО «АрселорМиттал Кривой Рог», Украина
Охрана здоровья и безопасностьИТОГИ 2008 годаОАО «АрселорМиттал Кривой Рог», Украина Фотоматериалы с мастер – класса по теме «Урок-соревнование, как тип урока с использованием игровых технологий при проведении тема
Фотоматериалы с мастер – класса по теме «Урок-соревнование, как тип урока с использованием игровых технологий при проведении тема 1254663
1254663 Теория и история религий
Теория и история религий 4. СОУЭ 2020
4. СОУЭ 2020 Загадки и чудеса Рафаэля
Загадки и чудеса Рафаэля Системы счисления
Системы счисления Второй год обучения. Весенний семестр.Тема: «Организация витрины и входа в магазин»
Второй год обучения. Весенний семестр.Тема: «Организация витрины и входа в магазин» Порядок осуществления эмиссии и обращения государственных и муниципальных ценных бумаг
Порядок осуществления эмиссии и обращения государственных и муниципальных ценных бумаг Семейный ужин
Семейный ужин Выносливость и её развитие
Выносливость и её развитие Общие должностные и специальные обязанности военнослужащих
Общие должностные и специальные обязанности военнослужащих Дворовый спорт в Заречье
Дворовый спорт в Заречье Раневые инфекции
Раневые инфекции Эволюция телефонной связи
Эволюция телефонной связи